It is very common to see how VPN services are offered as the definitive tool to guarantee our privacy and anonymity in the network, but nothing is further from reality,
many of them are leaks that can compromise our privacy
. For this reason, I think it is necessary to know
how to check the security of a VPN
and thus ensure that it does not filter our information.

When we say that a VPN exposes our information, we refer to parameters such as:
IP, DNS, geographic location, operating system, ISP (provider and internet), etc.
Although it may seem a lie, many websites store all this data when we visit it, so using a
VPN server
will help us protect our anonymity.
Steps to verify that a VPN is secure and does not filter our information.
Unfortunately there is no reliable and simple tool that allows us to audit the security of a VPN, so we will have to resort to different methods and programs for it. We also have a small article where we compile a
list of the VPNs that we should avoid
and that have already starred in some scandal or security breach.
Verify that the VPN does not expose our public IP.
First of all we must verify that it does not expose our IP.
For this, we can use the tutorial in which we explain
how to obtain the public IP from the terminal
(valid for Windows and Linux)
. If we use a VPN that encrypts all our traffic, it should not show our real public IP.
If we use an extension for the browser
(very common in free VPNs)
, we will have to use pages such as
http://icanhazip.com
to verify that our IP is not shown.
It should be clear that these extensions usually only encrypt HTTP traffic and are limited to browser use.
Verify that the VPN does not expose our DNS.
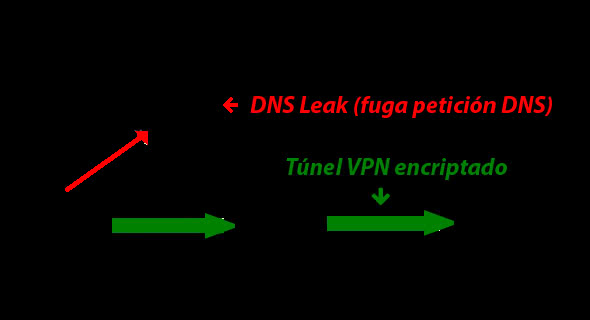
This section includes a security problem known as
"DNS Leak"
, which consists in exposing our DNS queries
(thus allowing us to record our activity).
In a slightly formal and simple way, we could say that DNS
(Domain Name System)
queries are responsible for translating a domain name to its corresponding IP.
This DNS query traffic must also be done through the VPN to ensure our privacy.
In this case, the simplest is to use pages such as
https://www.dnsleaktest.com
to verify that the DNS of our provider is not exposed.
To encrypt our DNS requests, a recommended option is to use the
DNSCrypt
protocol. This protocol improves security and privacy by
encrypting all DNS traffic between the user and the DNS server
.
Verify protocols and applications.
We live in an era in which free VPNs are quite successful, but many of them do not offer total security. As we saw that our IP can be filtered or DNS leaks,
when we use protocols such as FTP or WebRTC, it may be that the VPN is not able to encrypt this type of traffic and expose the data of our connection
.
The same can happen with messaging or P2P applications for file sharing.
In all these situations there is no simple method that tells us if we are exposing the data of our connection, so we will have to find out the form for each specific situation. I encourage you to use
our forum
to ask any questions that arise about how to check the security of a VPN or if a specific application is filtering your data.