Detailed analysis of vulnerabilities must be a key in any process that is carried out in all types of organizations because in a way we all have files and elements that can suffer some kind of attacks. Many are personal files and others of a corporate nature but each with a level of privacy and that is why it will be key to have not only security policies but also utilities that help improve security in any environment. Here comes into play OpenVAS of which TechnoWikis will tell you in detail.
What is OpenVAS?
OpenVAS has been developed as an integrated vulnerability scanner with numerous functions that allow optimization of the analysis and error detection processes.
Analysis that OpenVAS can perform
Within the analyzes that OpenVAS can perform we have:
- Analysis of unauthenticated tests and authenticated tests.
- Analysis of industrial and Internet protocols of high and low level.
- Ability to perform a performance adjustment for large-scale scans.
- Integration of an internal programming language thanks to which it will be possible to implement many more vulnerability tests in the environment.
OpenVAS has been tested with more than 50,000 vulnerability tests which gives us a guarantee of its capabilities and scope.
Functions
Greenbone Networks has been developed focusing on different levels of security and functions such as:
- GSA (Greenbone Security Assistant) which is the GVM web interface
- GVM-Tools which allow batch processing or scripting through GMP
- The OpenVAS scanner itself
Now we will see how to install OpenVAS on Kali Linux 2020 and thus add more security to the daily actions in the system.
How to install OpenVAS on Kali Linux 2020
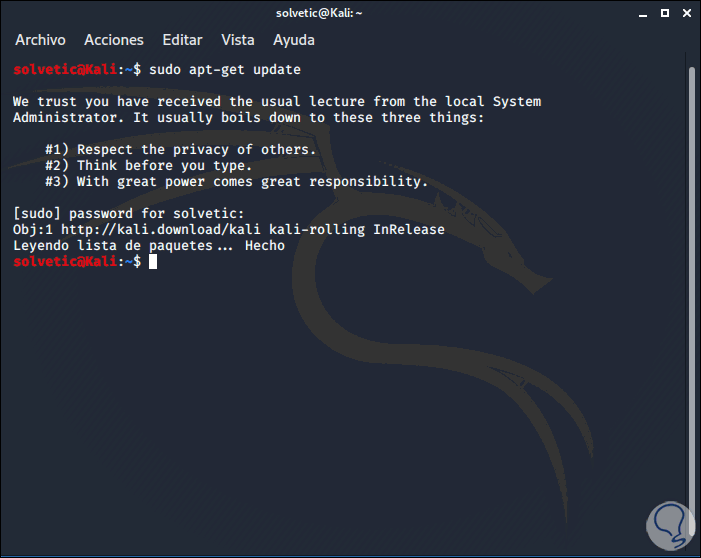
Step 1
The first step to take will be to update the system packages, for this we will execute the following:
sudo apt-get update
Step 2
After this we validate new updates of the general distribution. For this we execute the following line:
sudo apt-get dist-upgrade
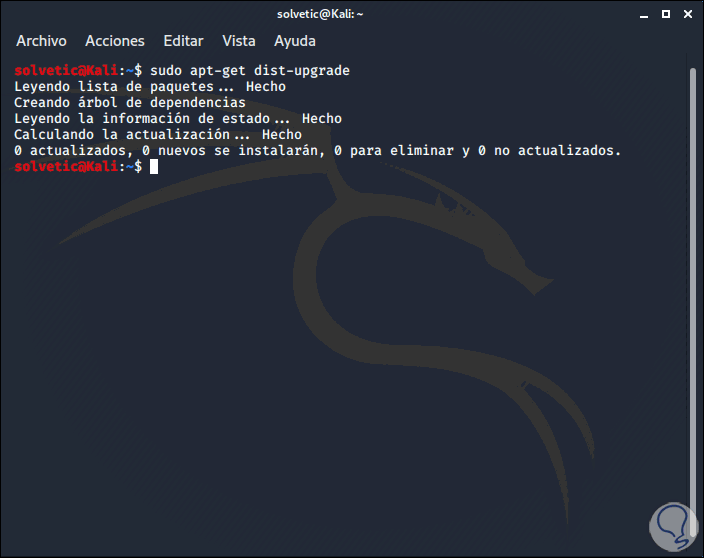
Note
This step is only necessary if we have versions prior to Kali Linux 2020.
Step 3
Once we have the most current edition we proceed to install OpenVAS with the following command:
sudo apt-get install openvas
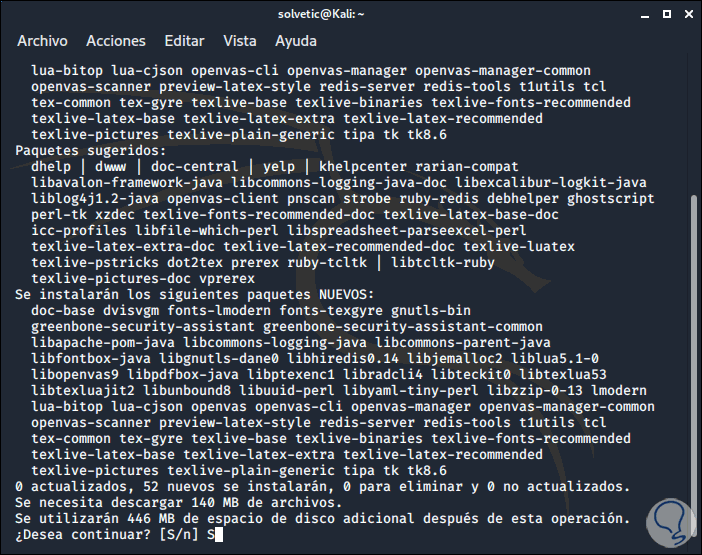
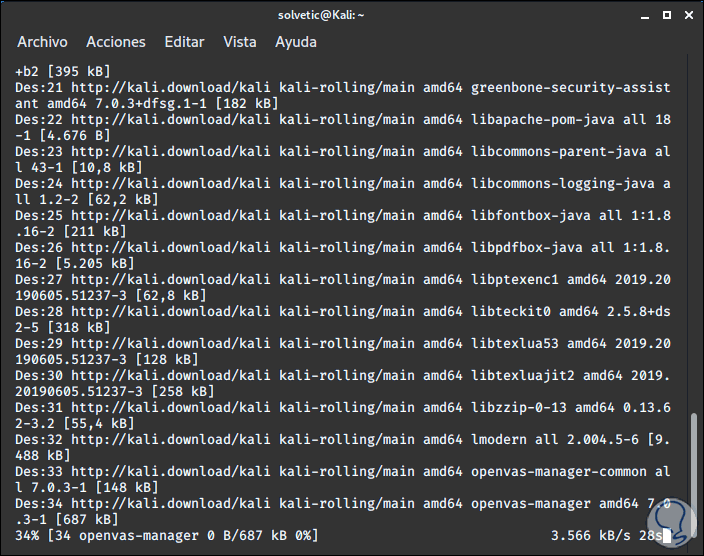
Step 4
Enter the letter "S" to confirm the download and the installation process of OpenVAS in Kali Linux 2020 will take place:
Step 5
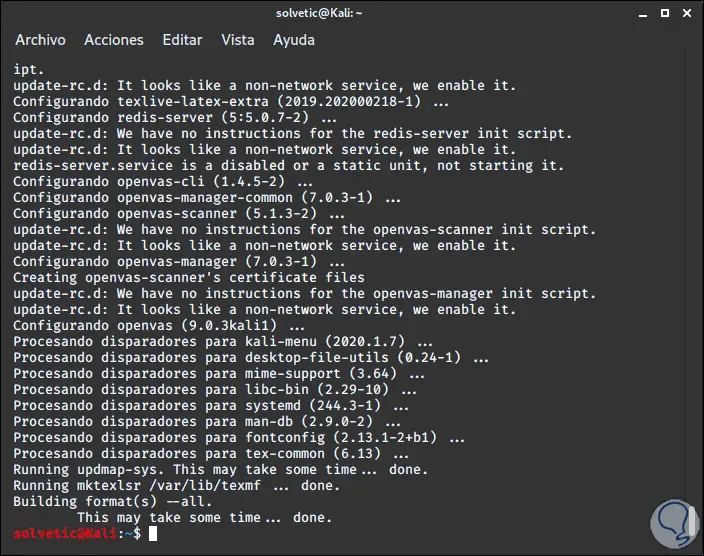
When it reaches its end we will see the following:
Step 6
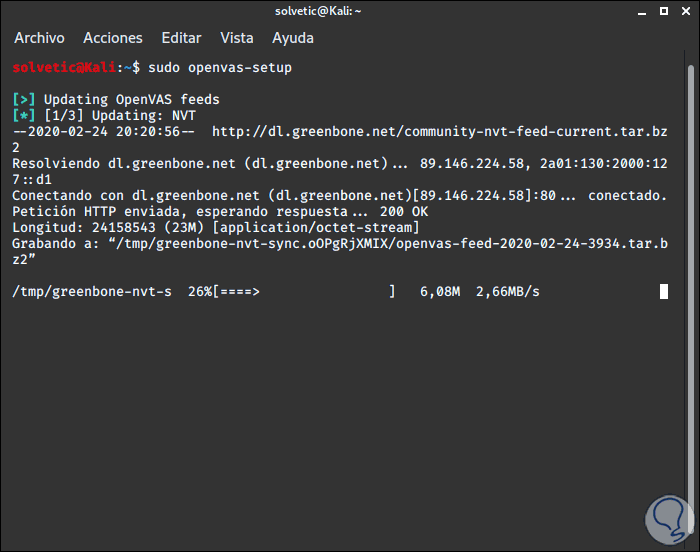
When OpenVAS has been installed in the system, we will configure OpenVAS, for this we execute the following:
sudo openvas-setup
Step 7
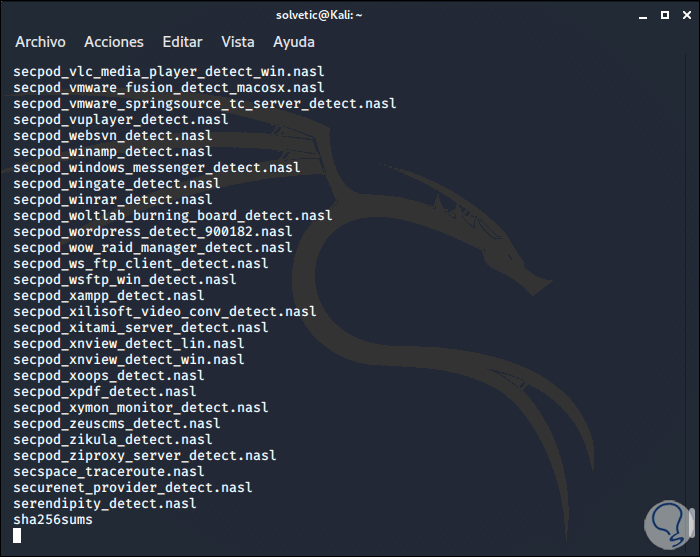
This will download all the processes necessary for the proper functioning of OpenVAS:
Step 8
When this process is finished we will see the following where a password is randomly generated for the created user:
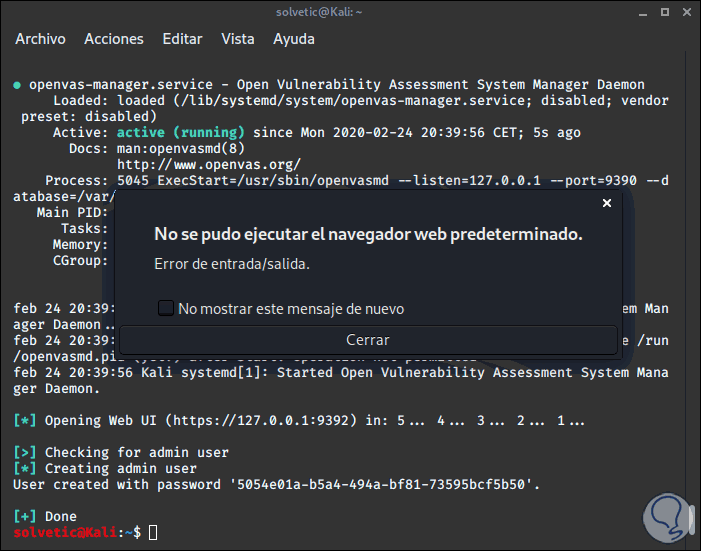
We recommend copying this password and hosting it in a place that we do not forget because it may be necessary later. As an additional point we can see the IP address with which you can access the OpenVAS graphical interface.
Step 9
Then we start OpenVAS by executing the following in the terminal:
sudo openvas-start
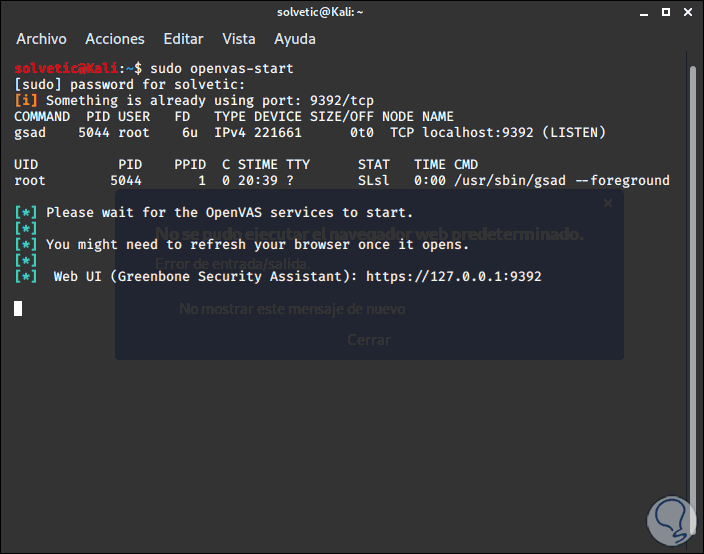
Step 10
There we access the web browser and enter the address:
https://127.0.0.1:9392
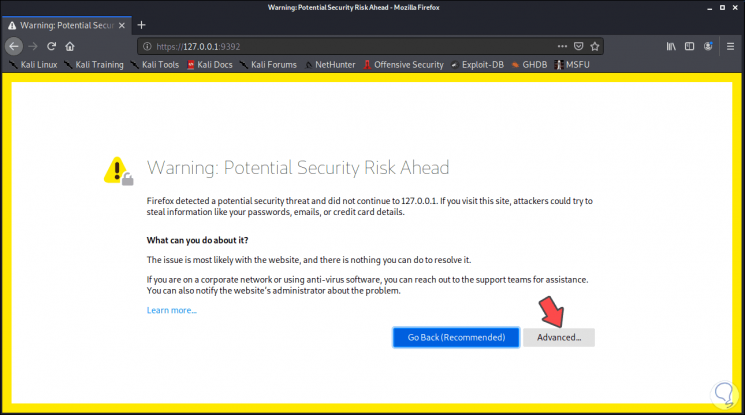
Step 11
We click on the "Advanced" button and then click on the "Accept the Risk and Continue" button:
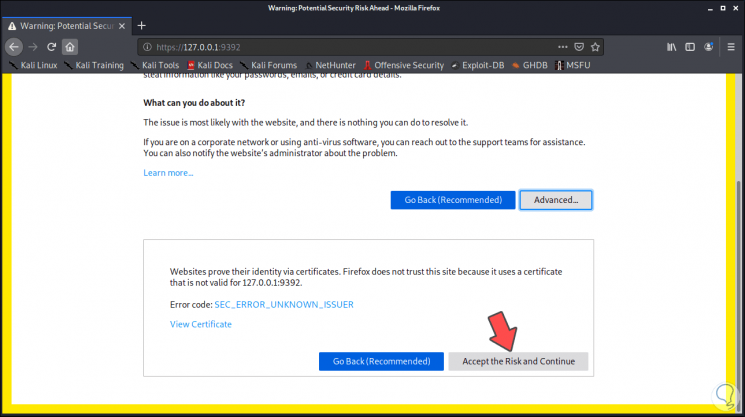
Step 12
This is due to browser security policies, by clicking there we access the OpenVAS login window which contains the user “admin†and the password that was generated during the installation:
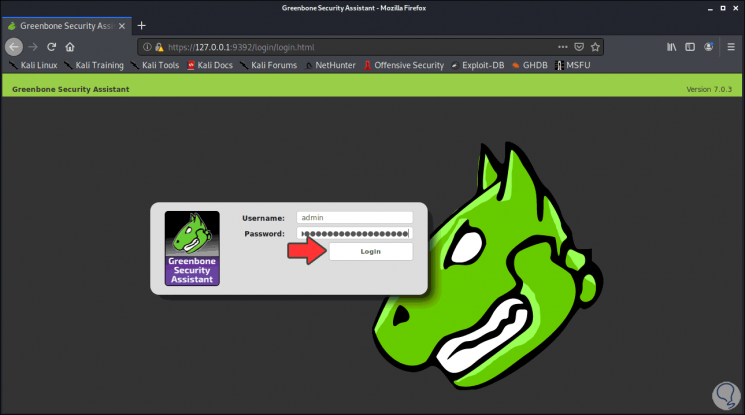
Step 13
We click on "Login" and access the OpenVAS console:
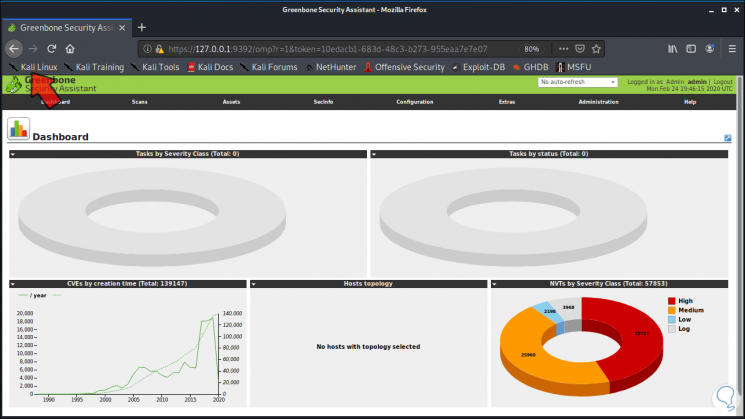
Step 14
From the Kali Linux menu we can administer OpenVAS in the "Vulnerability Analysis" section:
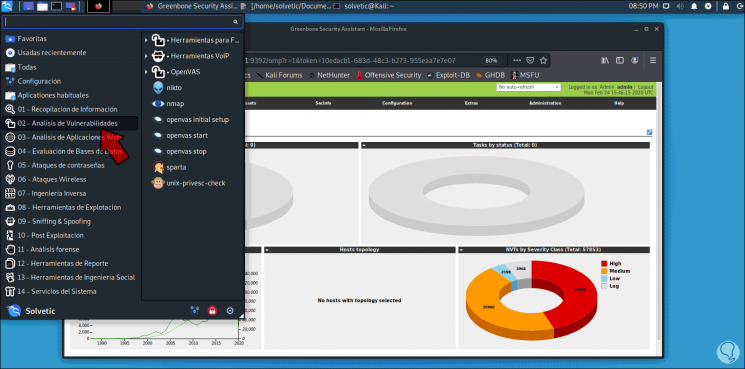
Step 15
We can see that OpenVAS displays some menus for use, these are:
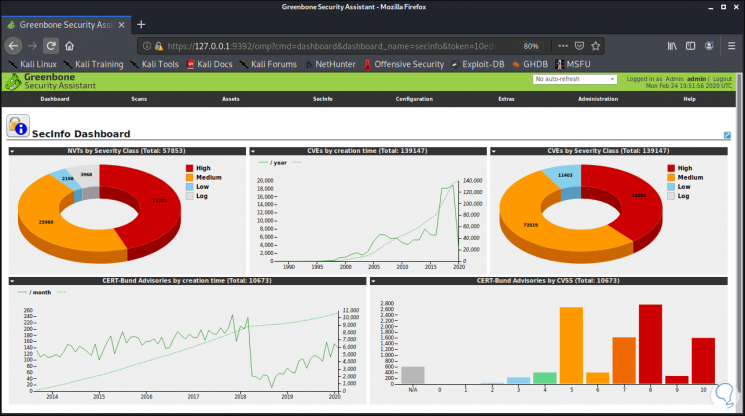
SecInfo
It is one of the most important since there we find all the security aspects of Kali Linux:
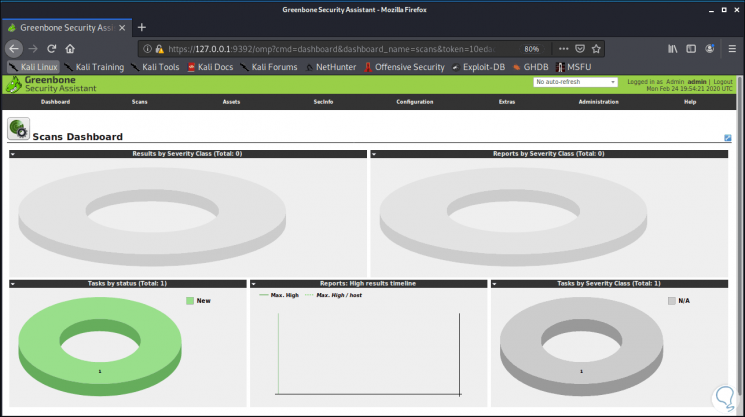
Scans
It allows us to see the scan tasks that have been executed or are scheduled:
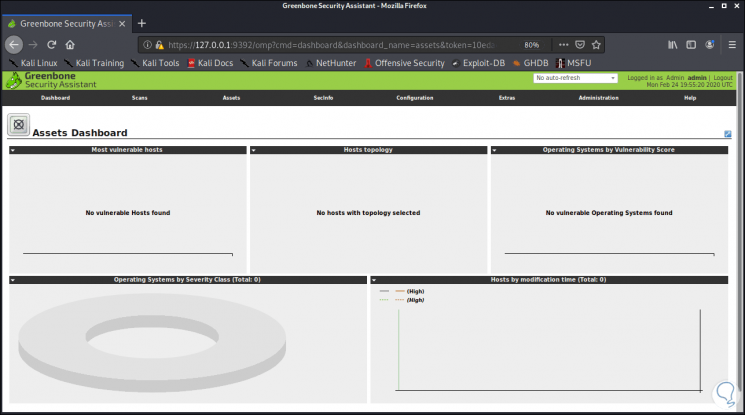
Assets
It allows visualizing the vulnerability of the components such as hosts or operating systems:
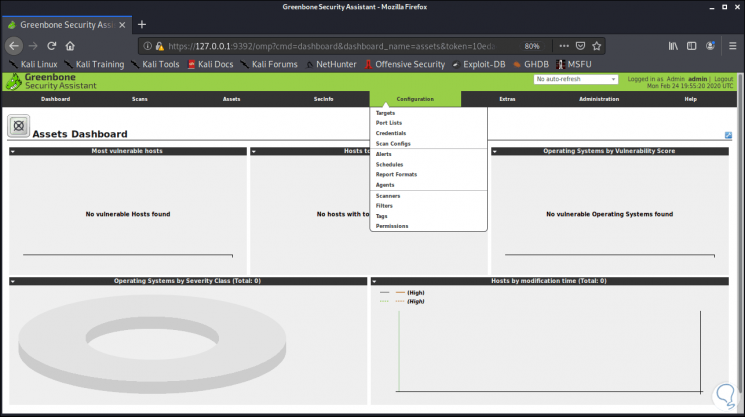
Configuration
It allows us to define the aspects that OpenVAS will use for the analysis and its access method. There we can manage objectives, credentials, scans, report format, alerts and more:
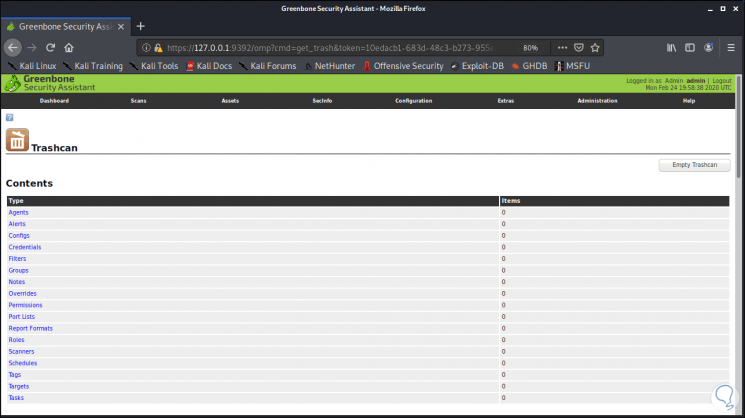
Additional features
Allows you to add general usage options to OpenVAS:
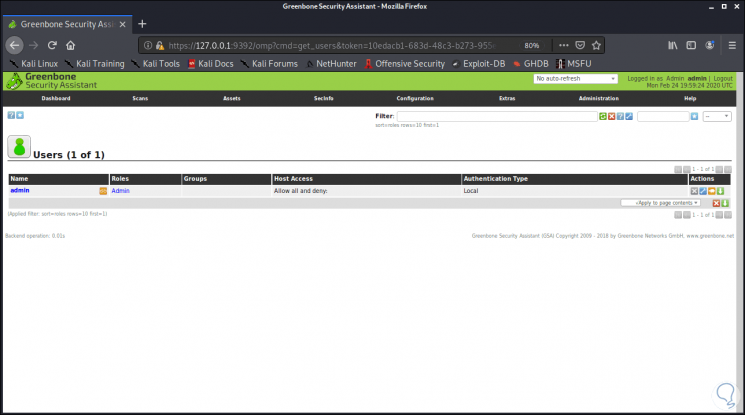
Administration
As the name implies, it allows you to manage passwords, users and more:
With OpenVAS it is possible to have a complete portfolio of options at hand to increase security in a system and validate its level of risk on the network.