In Linux we have a series of commands available to manage numerous aspects of both the operating system itself and the applications and other features and they are developed to provide us with precise administration, a delicate section is the network commands and in them we highlight one in particular that is the nslookup command. That is why we will tell you how interesting it is to get to install nslookup on Linux and thus be able to make queries about servers..
Nslookup Syntax
Nslookup is in charge of consulting the Internet name servers using an interactive method, its use syntax is the following:
nslookup [-option] [name | -] [server]
Nslookup gives us the opportunity to query Internet domain name servers using two available modes that are interactive mode and non-interactive mode, with interactive mode it will be possible to query name servers in order to access information from various hosts or computers and domains or print a list of computers in a domain if necessary while with the non-interactive mode we can only see the name and the required information of that host.
TechnoWikis will teach you how to install and use nslookup on Linux, for this case we will use Ubuntu..
To stay up to date, remember to subscribe to our YouTube channel!
SUBSCRIBE ON YOUTUBE
How to install and use nslookup on Linux
Step 1
We open the terminal and install nslookup by running:
sudo apt install dnsutils
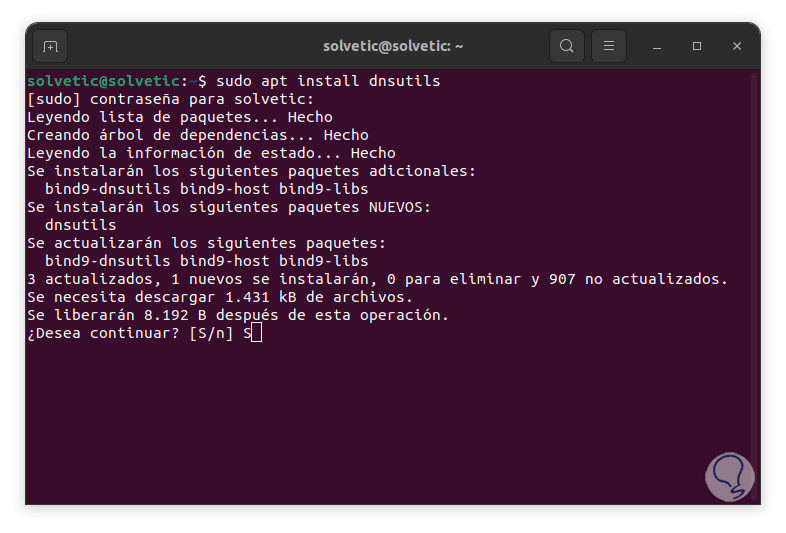
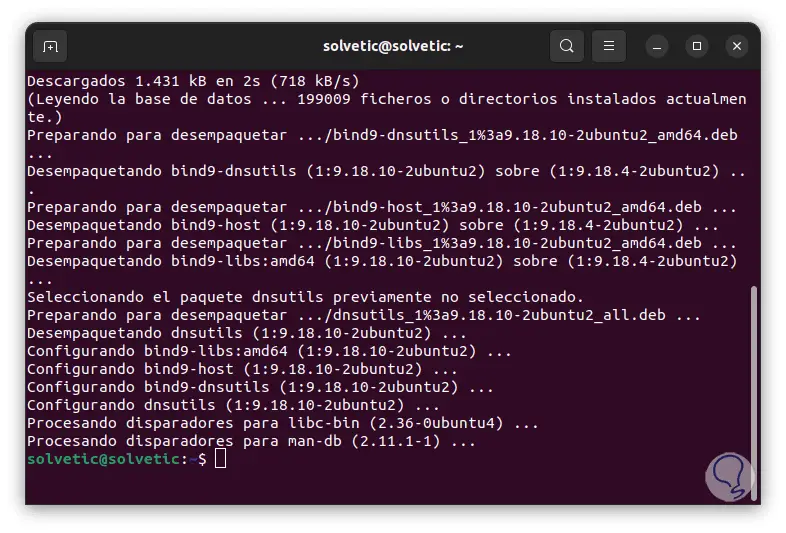
Step 2
We enter the password and accept the installation with the letter "S":
Step 3
To install it on CentOS, Fedora or RedHat we execute:
sudo yum install bind-utils
In the case of ArchLinux we use the command:
pacman -Sy dnsutils
Step 4
We run a basic search with the syntax:
nslookup (domain)
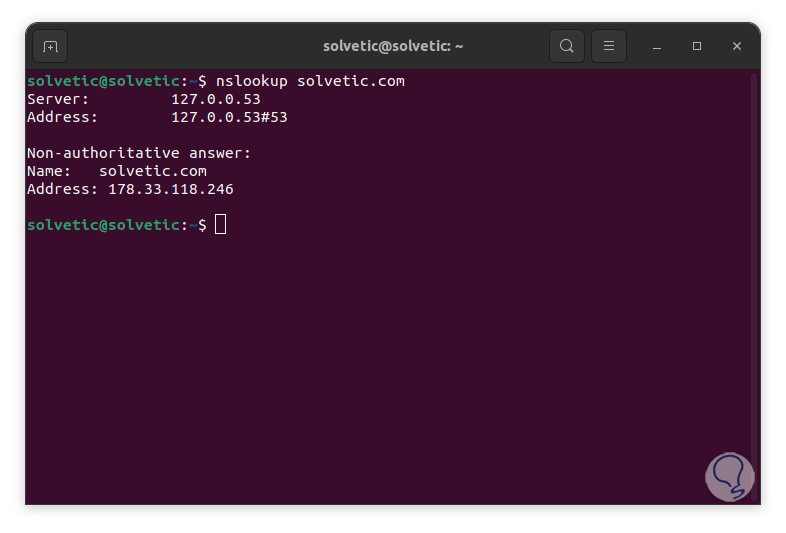
step 5
We see the result with some data, first we can see the server and the address that has been used by nslookup (nslookup will use the DNS server configured in the system by default), there we find the final port number which is used for the DNS queries and as such is the standard port for DNS queries on Linux, the Non-authoritative answer line refers to the fact that the response received by nslookup did not originate from the authoritative DNS server for the domain itself, this response will be hosted in the cache and then be forwarded from the local server where the query was executed, then we can see the DNS records of the domain name that we have indicated, there the A (Address) record is where the IP addresses for the name of domain and N (Name) the name of the domain.
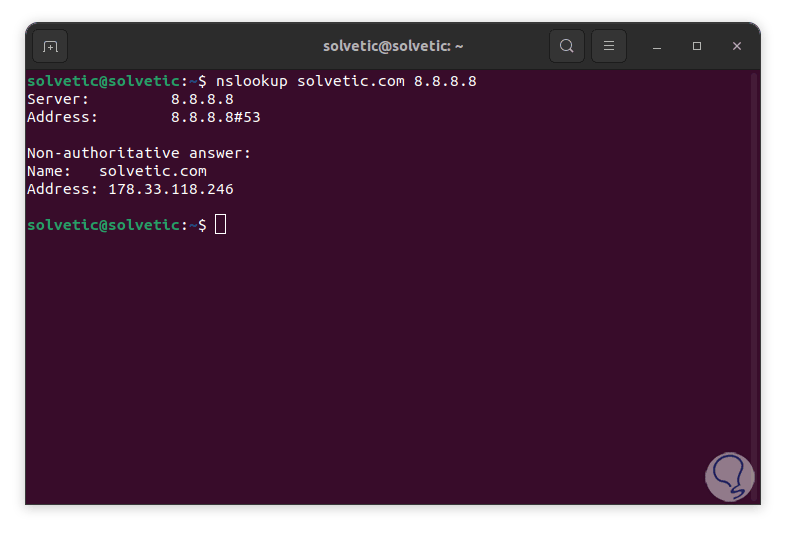
It is possible to add a DNS server in the query, it can be public or private if you have paid for it:
nslookup (domain) DNS
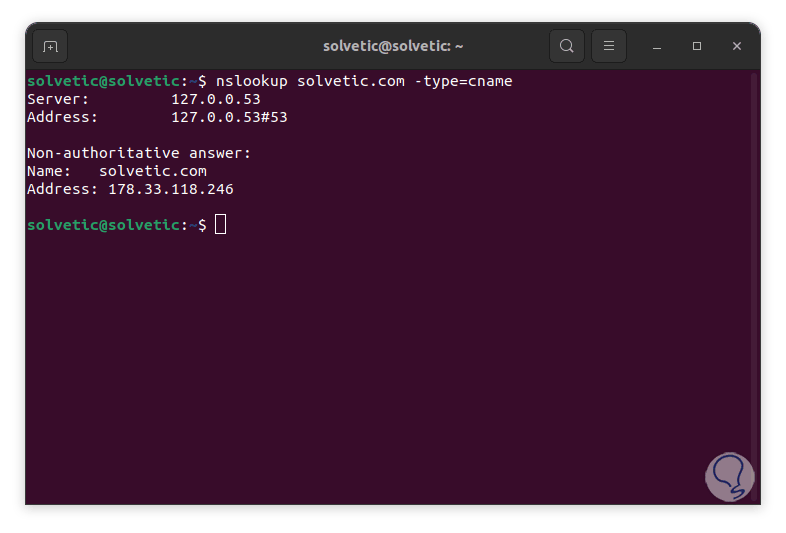
step 6
We can indicate the type of resources or records to use, for example:
nslookup (domain) -type=cname
step 7
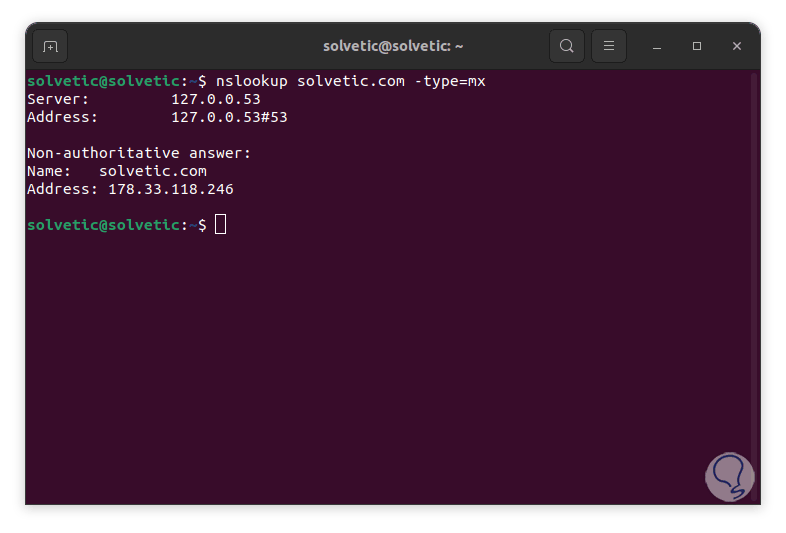
We can use another criterion:
nslookup (domain) -type=mx
step 8
The options to use are the following:
- A: Address Record, this is responsible for assigning a domain name to an IPv4 address
- AAAA: IPv6 Address Record, allows you to assign a domain name to an IPv6 address
- CNAME: Canonical Name Record, its function is to assign an alias to a real domain name when executing some remote access actions
- MX: Mail Exchange Record (Mail Exchange Record), as its name indicates, this will assign a domain name to an email server with which we can verify that email has been configured the way it is
- NS: Name Server Record, is a very important one as it assigns a domain name to a DNS server and indicates which DNS server is responsible for a domain it also records the locations of the domain's DNS records
- TXT: Text Record, this will house text information for a domain
step 9
To consult all the resources we execute:
nslookup -type=any (domain)
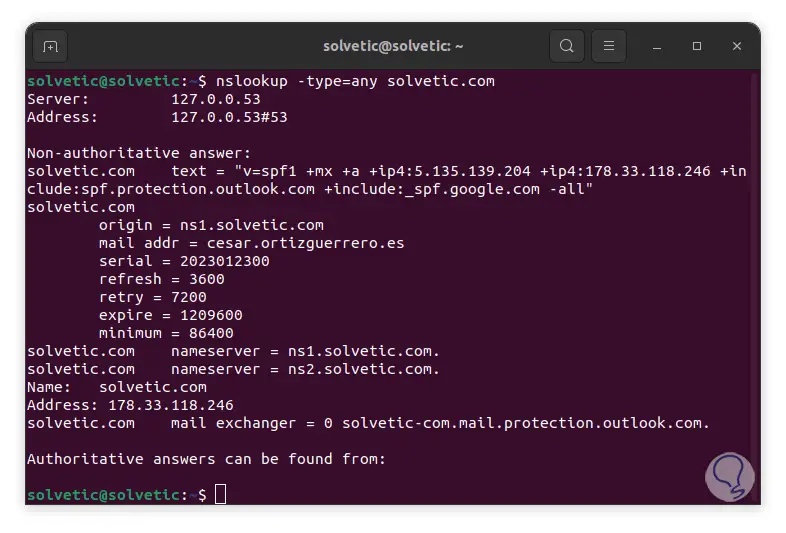
step 10
In this we will display all the necessary information.
Now, it is possible to query the DNS servers in order to access information about a particular IP address, this is called a reverse lookup, to run a reverse lookup using nslookup we execute the following:
nslookup (IP)
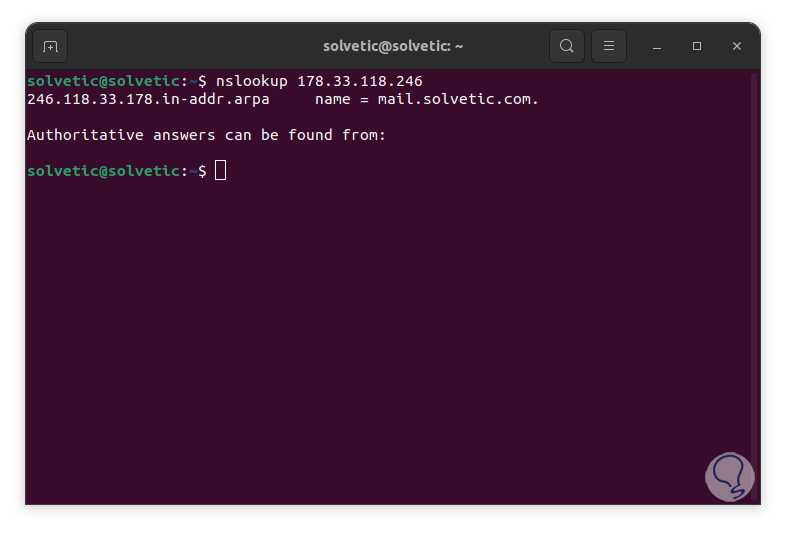
step 11
There is an administration option (debugging mode) with which it will be possible to access more information about DNS queries, it is ideal for a detailed analysis of what happens internally, to use debugging mode we execute:
nslookup -debug (domain)
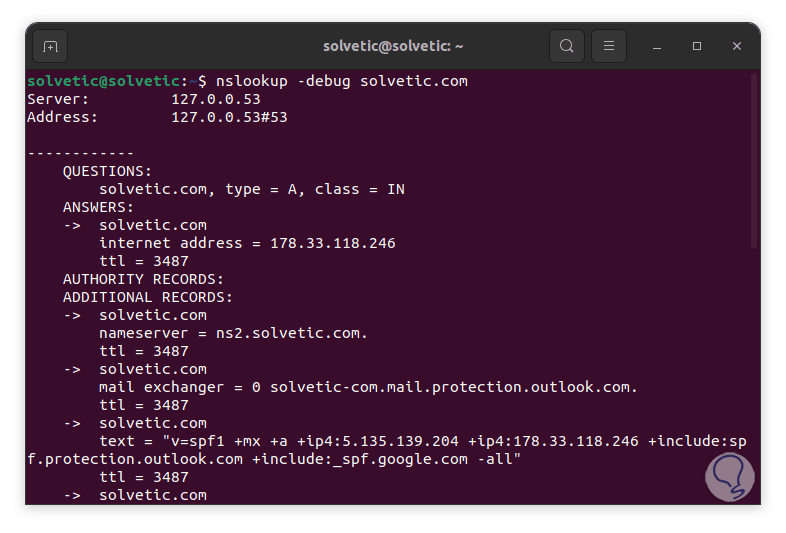
step 12
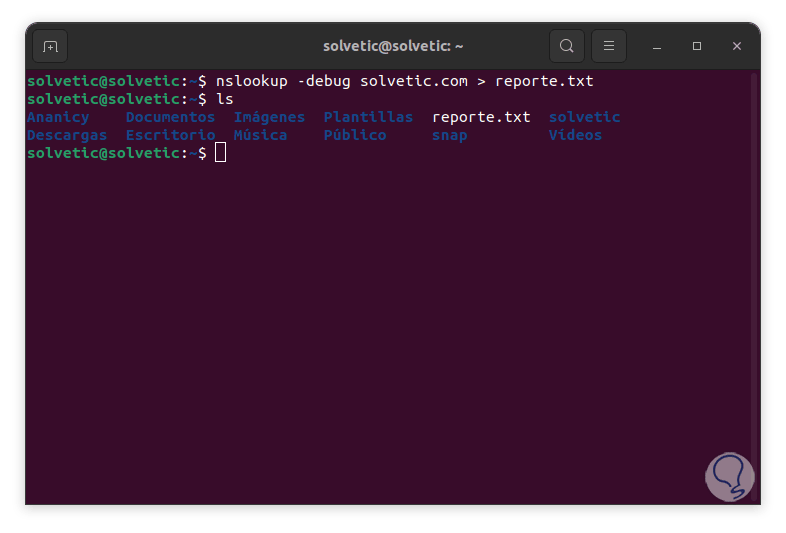
We can find much more specific details of the indicated domain. It is possible to export the result to a file, for this we execute:
nslookup -debug (domain) > file.txt
step 13
We use "ls" to see that it was created correctly:
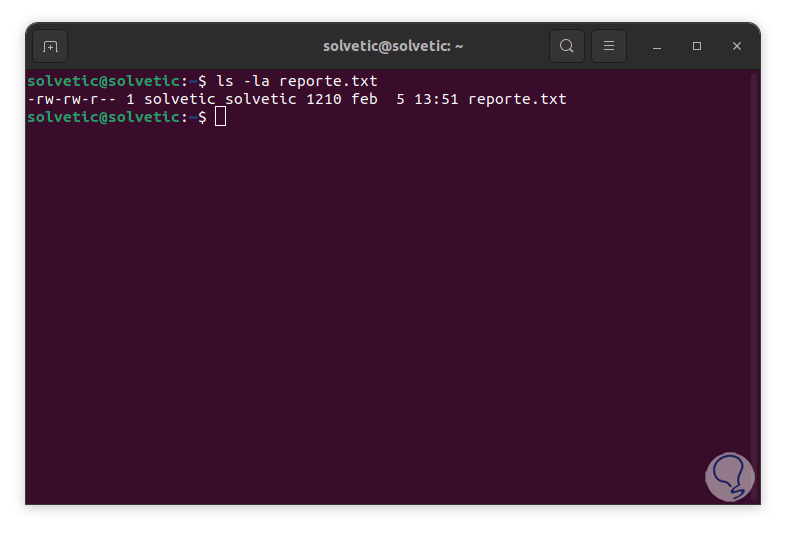
step 14
We validate the file permissions by executing:
ls -la file
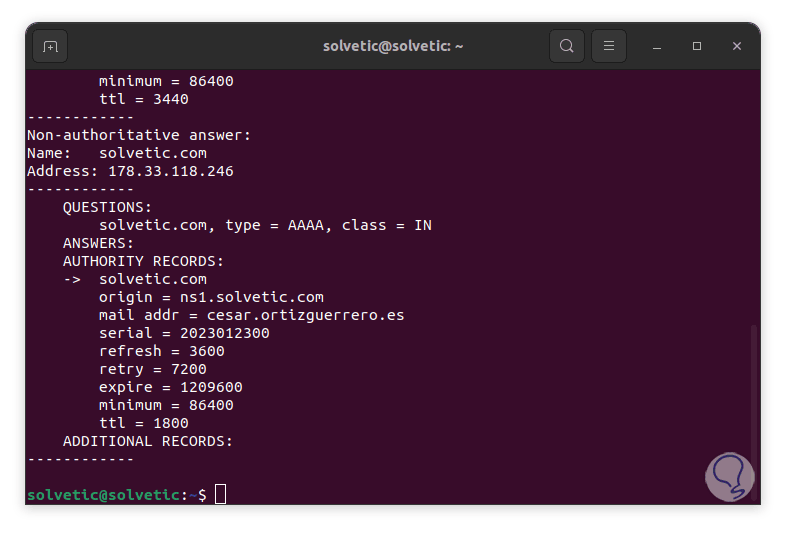
step 15
We visualize the created file:
cat file
step 16
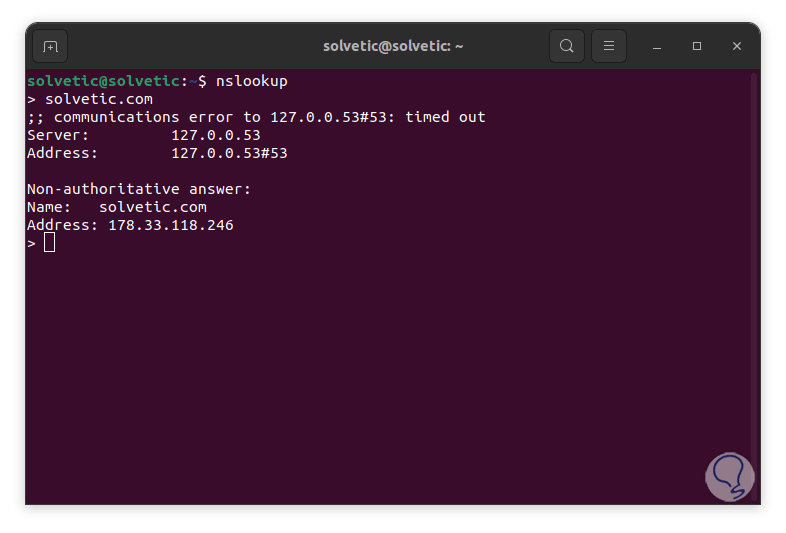
As we mentioned, the interactive mode is available, with this interactive mode it will be possible to execute various commands to query DNS servers without it being necessary to write the nslookup command directly, this can help save time, to use the interactive mode execute:
nslookup
step 17
In the terminal we enter the domain to search and the results will be launched:
Thanks to the nslookup command, we will be able to carry out general control over a domain, either in a basic or complete way, using the available parameters and thus accurately determine each aspect that is made up of network communication.