The protection of information security is more than essential and important in the current business environment, in the introduction to business information security, the important points to take into account to take business IT security seriously today were already seen. ..
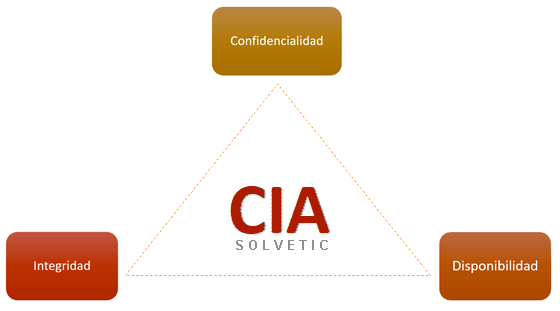
Information is valuable and sensitive, it always has been, it is nothing new and less at a business level, that was what was explained in previous chapters, such as the introduction to Information Security for companies, but now we have it in digital format and for it is in constant risk of exposure, alteration or loss. To ensure adequate protection of information, it is necessary to initially understand and be able to apply the basic principles of information security. These are known as the CIA triangle, which is made up of three principles: Confidentiality, Integrity and Availability.
If we want to start the strategy to face the security of business information in order, we must not forget these principles. The protection of an organization's digital assets should be one of the main points to be addressed in an agile and orderly manner in order to be more successful in preventing this type of risk..
From a technical point of view, the three principles of information security are essential to protect the company's digital assets, guarantee the continuity of its day-to-day operations and maintain customer trust because the good security image in this regard It is vital for the trust of customers and business partners with which the company regularly operates. Computer security principles must be protected together if we want to achieve effective protection of business information and not get scared. The three principles go hand in hand. Not protecting any of them would ultimately leave all three together as a weak point.
We explain below the importance of the different information security protection principles , in addition to the recommended actions to be applied in each one..
Importance of Security Protection Principles: CIA
Confidentiality is essential to protect important company data, intellectual property, company financial information and employee personal data, as well as customer data. As we said before, the unprotection of this data can cause serious damage to the company's reputation, a loss of competitive advantage and even possible legal penalties. From a technical point of view, maintaining confidentiality requires the implementation of measures that we will explain below.
Integrity is important to ensure that company data and systems are reliable against unauthorized modification and misappropriation. An unauthorized alteration of company data (by misuse of employees unconsciously or maliciously by internal or external people) can have negative consequences in decision making, operational efficiency and quality of the product or service offered to customers and partners. Technically guaranteeing it is important, and you must have knowledge of security to have updated systems and policies in this regard. In addition to performing actions that we will define later. Ensuring authenticity is the goal of integrity.
Availability is also considered important to ensure that systems and information are always accessible to authorized users of the company when and where they need it with minimal security risks. That the systems are scalable and can adapt to the growing demands of the company is one of the points that every company should take into account to successfully carry out the principle of availability.
If we do not provide security in the availability of the company, it could affect it, generating interruptions in its daily operations and that would imply loss of productivity, drop in income, loss of reputation, etc. Technically, maintaining availability is going to require actions that we will detail below.
The joint consideration of these three principles in the technical approach to information security allows a comprehensive approach to the threats and vulnerabilities that a company faces. Each of these principles is mutually reinforcing, and a weakness in one of them can have a negative impact on the other two. For example, if the confidentiality of the data is compromised, the integrity of the information may also be affected, since attackers could modify the data without authorization. Similarly, if systems are down, sensitive information could be exposed to additional risk.
Ultimately, it is critical that companies take a holistic technical approach to information security, considering the importance of confidentiality, integrity, and availability in their data protection strategies. This implies not only the implementation of technologies and processes.
confidentiality

Confidentiality is the protection of information from unauthorized access or disclosure. The purpose of this principle is to ensure that information is only available to those users who have permission to access it. The fact of limiting access to each type of information to only the teams or people who must have access to it is a basic principle that is often violated within organizations. Confidentiality is also important so that user privacy, intellectual property, and sensitive business information are not compromised.
We will see some of the actions to guarantee confidentiality, organizations can implement measures such as:
1. Policies and procedures related to Confidentiality.
2. Role-based access control and user authentication.
3. Encryption and protection of data and communications.
4. Train employees on the importance of confidentiality of information and how to practice it at the corporate level. In addition to Legal and regulatory compliance based on privacy and data protection.
Integrity

In a quick plan, integrity is the protection against unauthorized modifications that can be received at the business level of both the information and the systems. Integrity can be violated through corporate accidents or maliciously, but both cases must be taken into account and actively protect it.
Integrity aims to ensure that the information is accurate, complete and reliable. It is essential to guarantee the quality and consistency that the data will offer and, above all, to maintain confidence in the business systems and processes that are used daily by all personnel.
To guarantee the integrity of the information, organizations can take actions such as the following:
1. Policies and procedures related to Integrity.
2. Control of access to data and use of company systems. (Authentication and authorization).
3. Conduct audits and monitoring focused on integrity. Such as monitoring and auditing of changes made to company data.
4. Maintenance and updates of systems in servers, equipment and business devices. Although it can be said that carrying out this action also applies to the other principles, in this case it will focus on a more secure integrity of the organization's systems and data, having everything updated, with the basic well-implemented security that this implies.
5. Make Backup Copies (Backup) of the company's data on a regular and well-organized basis that guarantees its recovery in the event of damage, loss or violation of part of the business information due to a computer attack.
6. Response to incidents (of those that affect integrity).
These actions are very important to maintain integrity, but the fifth point is really vital that it be carried out correctly, because by doing it, you can have the option of recovering the data carried out and used by the company, in addition to not affecting its operations, being able to to the total blocking of the company in case of not having these backup media.
Availability

This principle of information security called: Availability, refers to timely and reliable access to information and systems by authorized users. The goal is to ensure that information resources and systems are available when and where they are needed quickly, effectively, but also securely.
Availability is key to the work carried out by the organization's employees, but its applied security is also key, so there must be a balance of access that does not generate unnecessary limitations or excessive blockages that greatly affect the company's productivity. To ensure data availability, organizations can implement actions such as the following:
1. Redundancy and distribution of the company's IT systems and infrastructure.
2. Capacity planning and workload management.
3. Disaster recovery and business continuity policies.
4. Plans regarding the availability and continuity of Business.
5. Training and awareness to maintain adequate availability of systems and data by the workforce.
As you have seen initially, in order to successfully implement these principles of business information security, it is necessary to carry out a series of actions that allow the effective application of confidentiality, integrity and availability. By rotating the actions between these three principles, we will surely be able to have a correct security structure at the business level of the data.
As you will have been able to verify that we commented on some actions, it is important to take into account that some may belong to more than one information security principle, this occurs because they are interrelated and in some cases they reinforce each other when applied to each of the beginning.
Ex: Monitoring and auditing is an action that is relevant to integrity and confidentiality. Policies and procedures may also apply to all three principles: confidentiality, integrity, and availability. It also happens with training, as different trainings have to be carried out for each principle and it can be applied all in one, in terms of training protecting several principles etc.
For all that has been learned, knowing the principles of information security protection at the business level is essential to prevent security breaches, protect sensitive data and maintain the reputation of the company. The proper implementation of these principles guarantees the confidentiality, integrity and availability of information. In addition, it helps to comply with legal regulations and industry standards, avoiding penalties and financial losses. Knowledge of these principles allows companies to identify and manage risks, adopt appropriate security measures and respond effectively to possible incidents, ensuring business continuity and the trust of customers and partners.